|
|
Over the last years, Trend Micro has seen significant
changes in the security industry, and likewise, we have been developing
internally to meet these new challenges presented by evolving threats, emerging
technologies, and our competitors. Inside Trend Micro, we are focused on better
serving our customers based on their needs, how they use computing technologies,
and how they are impacted by an ever-changing threat landscape - customers will
come to know Trend Micro as a friendly, knowledgeable partner to help ensure
their computing security through flexible and customizable solutions. As the network has expanded, our protection
strategies must also expand. Trend Micro is staying at the forefront of
protection methods with new In-the-cloud services, and by analyzing the root
causes of information leakage designed to prevent information-stealing malware
from entering into a user's information flow.
Our goal, as it has been for
years, is to help create a world safe for the exchange of digital information.
|
|
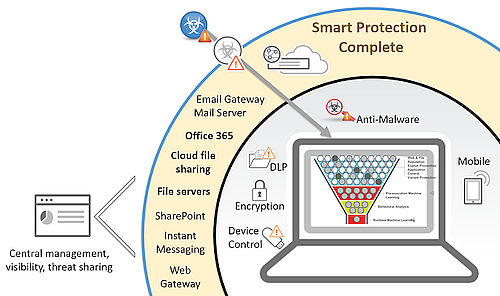
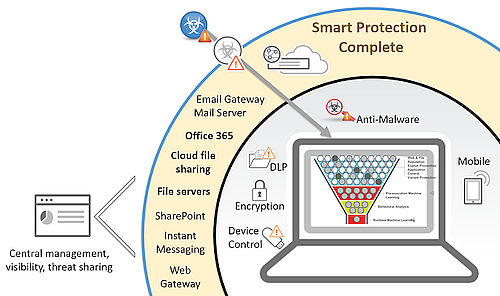
Trend Micro Smart Protection Complete
Trend Micron laaja tuotepaketti kattaa perinteisen suojauksen lisäksi erittäin kehittyneiden next generation -uhkien torjunnan.
- Sähköpostin, Office 365:n ja monien muiden tiedostonjakopalveluiden tietoturva
- Päätelaitteiden ja mobiililaitteiden suojaus ja hallinta
- Tietovuotojen esto, kiristyshaittaohjelmien, johtajahuijausten sekä haavoittuvuuksien hyväksikäytön esto
- Suoja vielä tuntemattomia uhkia vastaan
Ratkaisu lisensoidaan per käyttäjä eli asiakas maksaa vain todellisista käyttäjistä.
Loppuasiakaskohtainen minimilisenssimäärä on Smart Protection Complete tuotteessa 101 käyttäjää. Laitteiden määrää ei ole rajattu.
Trend Micro on päätelaitteiden tietoturvaratkaisuiden globaali markkinajohtaja ja edelläkävijä 30 vuoden kokemuksella. Suojaamme maailmanlaajuisesti yli 500’000 organisaation ja miljoonien kuluttajien toimintaa edistyksellisillä tietoturvaratkaisuillamme. |
Trend Micro Smart Protection Complete
Complete user protection provides better, simpler, more flexible security
Traditional security solutions can’t keep up with your users. Turning to multiple point
products to address the myriad of challenges only increases complexity and may leave
gaps in your security. Plus, you need a flexible solution that can grow and change with
you as you migrate from on-premises to the cloud. To effectively counter today’s evolving
threat landscape, you need integrated security that consolidates your view across all
layers of protection and all deployment models.
Trend Micro Smart Protection Complete is a connected suite of security capabilities that protects
your users no matter where they go or what they do. This modern security delivers the best
protection at multiple layers: endpoint, application, and network, using the broadest range of threat
protection techniques available. Plus, you can evolve your protection along with your business
using flexible on-premises, cloud, and hybrid deployment models that fit your IT environment
today and tomorrow. In addition, you can manage users across multiple threat vectors from a
single “pane of glass,” giving you complete visibility of the security of your environment.
Multiple layers of connected threat protection
This comprehensive suite integrates security across protection layers with flexible cloud deployment,
simplified licensing, and central management for network-wide visibility and control of threats and
data. The following layers of security are included in this suite:
- Endpoint Security. Secure user activity on physical and virtual desktops, laptops, or
mobile devices with threat and data protection, application control, vulnerability protection,
and encryption.
- Mobile Security. Secure, track, monitor, and manage your employees’ mobile devices and
company data with mobile security that balances consumerization with IT control.
- Email and Collaboration Security. Get superior protection against spam, phishing,
malware, and targeted attacks at the mail server, gateway, and for cloud-based applications
like Office 365.
- Web Security. Protect your users’ web activity on any device in any location. They gain secure
access to the latest web and social media applications, and you get complete visibility and control
of employee web usage in a cloud-based SaaS or on-site secure web gateway solution.
- Centralized Security Management. Manage multiple layers of connected threat and
data protection for complete, user-centric visibility across the entire threat lifecycle.
ADVANTAGES
Smarter Protection against today’s evolving threats
The broadest range of advanced threat protection techniques and protection points secures all
user activities, reducing the risk of information loss.
- Endpoint security: Secures physical and virtual endpoints using the broadest range of threat
and data protection techniques across all devices and applications.
- Advanced threat protection: Includes integrated threat sandboxing, Command & Control
detection, browser exploit protection, application control, behavior monitoring, ransomware
protection, memory inspection, web threat protection, vulnerability protection, and host
intrusion protection.
- Mobile security: Secures, tracks, monitors, and manages your employees’ mobile devices and
company data with mobile device management (MDM) and data protection.
- Email and collaboration security: Secures real-time collaboration and stops targeted attacks,
spam, phishing, viruses, spyware, and inappropriate content from impacting your business.
Security for the email server, gateway, collaboration portal, instant messaging, and cloud-based
applications such as Office 365.
- Secure web gateway: Protects users from web-borne threats and provides granular control and
visibility of web usage.
- Endpoint encryption: Ensures only authorized eyes can see your information.
- Centralized management: Provides comprehensive view of user security to let you analyze
data and threats across the whole solution.
- Integrated, template-based data loss prevention: Ensures information is protected at the
endpoint and across multiple layers.
- Lightweight and optimized security: Ensures no impact on device, application, or
network performance.
- Real-time connected threat intelligence: Correlates threat data from our global threat
intelligence network.
- 24x7 support: Means that when a problem arises, Trend Micro is there to resolve it.
|
|
Download
Free Trials
|
 |
|

|
|